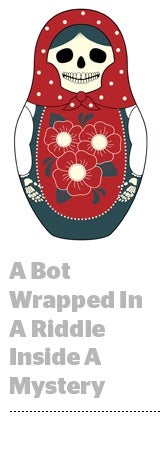
 Meet Methbot, the Russian hacking operation that’s costing advertisers between $3 million and $5 million a day.
Meet Methbot, the Russian hacking operation that’s costing advertisers between $3 million and $5 million a day.
At the very least, that’s a little over $1 billion a year – a hefty chunk of the ad industry’s estimated $7.2 billion annual ad fraud problem.
White Ops first uncovered the browser-based botnet in September 2015, when it was a minor operation, and continued tracking its evolution and various iterations through October 2016, when it started to ramp up its volume significantly.
Methbot’s fraud of choice: gaming high-CPM full-size video inventory.
(The name “Methbot” is a mystery. It appears to be the name the hackers themselves chose for their creation. White Ops noticed it woven into the code of the botnet’s malware signature.)
White Ops consulted with digital analytics and programmatic media intelligence company AdFin to figure out the real value of the inventory on the sites being spoofed by Methbot – an average CPM of just over $13.
By combining that information with the amount of traffic it was observing, White Ops estimated that Methbot was sucking up between $3 million and $5 million a day in US ad spend.
The bad actors behind Methbot clearly have a deep and highly developed understanding of how the programmatic advertising ecosystem operates.
“It was layers of sophisticated on top of layers of sophistication – it blew us away,” said White Ops CEO and co-founder Michael Tiffany, with grudging professional admiration for his adversary.
Most botnets comprise a network of real people’s computers that are infected by malware, with cybercriminals at the helm, so perpetrators have to infect new computers when their malware is discovered.
Methbot took a different approach, forging nearly 600,000 IP address registrations and associating them with internet services providers in the US – including Verizon, Comcast and Spectrum – to make the traffic look like it was coming from real homes spread out across America.
The bot operators created more than 250,000 fake web pages with counterfeit inventory from over 6,000 top-line publishers, including The Economist, The Huffington Post, Vogue, ESPN, Fox News and CBS Sports.
The fake sites were very convincing. The browser’s address bar was rigged so that anyone looking at it would see what seemed like a legitimate URL.
The automated Methbot browsers generated between 200 million and 300 million bogus video ad impressions per day and faked clicks, mouse movements and social login information as a way to hoodwink anti-fraud vendors.
A lot of this activity took place on the open exchange, which gave Methbot the cover it needed to commit its crimes. Methbot also insinuated itself into private marketplace deals, which are generally believed to be fraud-free and more brand-safe.
Because there aren’t authorized reseller programs for online inventory, no one bats an eye when various third parties and ad networks have access to inventory from primo websites – or what appear to be primo websites, said Tiffany.
 “The Methbot operators take advantage of that fact,” he said. “The ultimate source of truth about where an advertising opportunity is happening is in the browser – but if you carefully rig the browser to lie about that, there is almost no defense.”
“The Methbot operators take advantage of that fact,” he said. “The ultimate source of truth about where an advertising opportunity is happening is in the browser – but if you carefully rig the browser to lie about that, there is almost no defense.”
That’s because the notion of “let the buyer beware” doesn’t apply here. Some publishers are duped into buying bad traffic, and some do it with their eyes open, looking the other way. But in this case, the publishers that were victimized had no idea their sites were being spoofed.
White Ops is working with the Trustworthy Accountability Group to coordinate an industry-wide action against Methbot. Although Tiffany was prohibited from going into details about their efforts, he was able to say that White Ops is “in contact with federal law enforcement.”
Fraudsters are generally nimble, slippery and anonymous. Catch them and they dissolve into the night, only to almost immediately set up a new operation. For the moment, the risk/reward ratio of ad fraud makes it a far more attractive playground than other more regulated areas like banking, credit card fraud or identity theft.
“Ad fraud is one of the few places where you can have recurring revenue for cybercrime with little risk,” said Tamer Hassan, CTO and co-founder of White Ops.
But although Methbot was an elite operator in this space, its sophistication is also its Achilles’ heel.
Falsifying and commandeering an army of hundreds of thousands of fraudulent IP address – the buttress propping up the entire scheme – is not easily replicable, Tiffany said. It took years for Methbot to ramp up, and putting it out of commission could turn off the spigot on around one-seventh of annual global ad fraud losses.
“When players in the programmatic space know to stop trafficking to these IP address, we’re going to be able to take this thing down – this operation will truly not be able to recover,” said Tiffany, who noted that White Ops is making all of the data it has on Methbot available on its website, including the 6,000 odd hacked publisher domains and roughly 600,000 compromised IP addresses.
But Tiffany declined to say whether law enforcement will be looking to prosecute the hackers. That could be a complicated process, considering that Methbot is an international operation, with data centers in Amsterdam and the US in addition to its headquarters in Russia.
Even if the specific hackers behind Methbot aren’t prosecuted, though, outing Methbot’s methods brings the industry one step closer to making ad fraud into a manageable problem.
“Measures like this alter the economics of bot fraud in a way that starts to make it unattractive,” Tiffany said. “How can we make a $7 billion problem shrink by many orders of magnitude so that it’s only a, say, $70 million problem? Some people will still do it, but it won’t attract genius-level operators.”
Genius-level operators using their ill-gotten gains for undoubtedly unsavory purposes. In essence, international crime indirectly funded by CPG brands, auto brands and brand name retailers.
“Sometimes, ad fraud is lumped in with other forms of waste or inefficiency or even quality issues, but it really is categorically distinct,” Tiffany said. “We’re not talking about dropping some money on the floor or whether there should be more ads above or below the fold. This is funding organized crime.”